In our days, it is very important to understand how IP addresses work, because we are so involved in this digital era. One of the IP address that has received most attention recently was 185.63.263.20. Even though it looks random when somebody reads it, it has been associated to some risks online.
Before we take the next step here, first we need to define what an IP address is. To simply define it an IP address is a series of numbers that uniquely identifies a computer or other device which uses the Internet protocol.
Next, we will examine why 185.63.263.20 has been associated with a couple of risks online. These risks could be used to threaten your service if you are not vigilant or inattentive.
This article intends to describe these risques and give some tips on how to protect yourself.
Table of Contents
About 185.63.263.20?
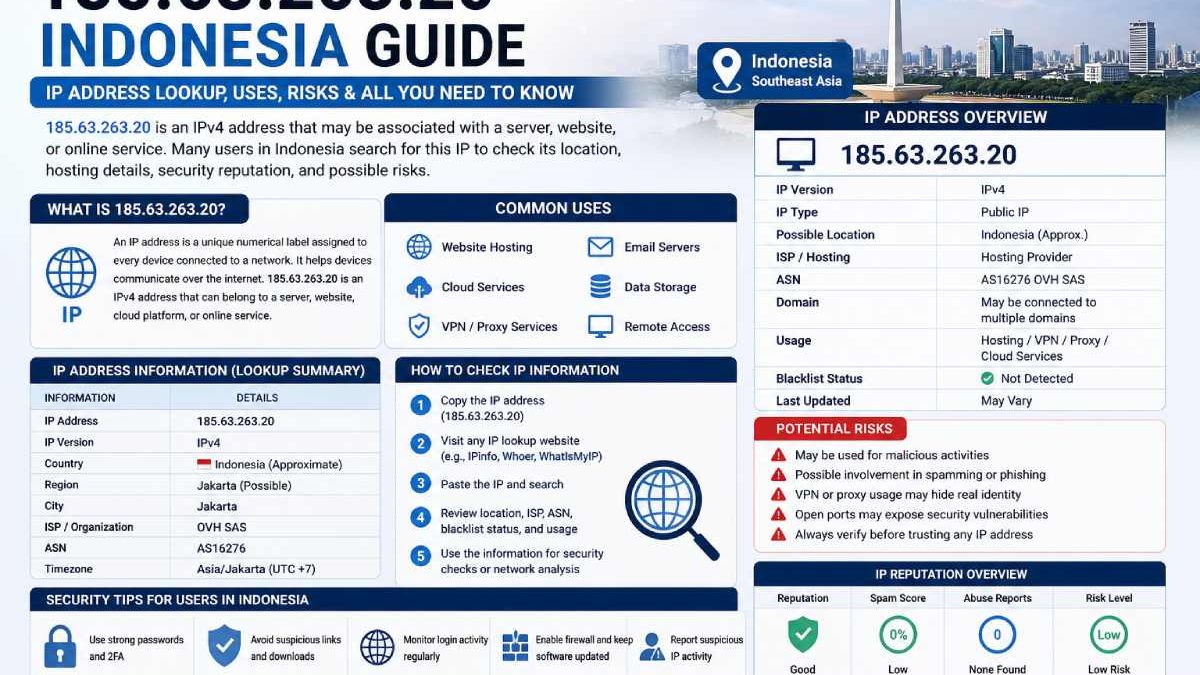
185.63.263.20 looks in the format of an IPv4 speech. Net Protocol (IP) reports are unique numerical identifiers assigned to servers, websites, hosting providers, or internet-connected devices.
An IP address will helps the route internet traffic between the devices and servers universally.
Basic IP Address Structure
| Component | Explanation |
| 185 | Network identifier section |
| 63 | Routing segment |
| 263 | Additional network allocation |
| 20 | Specific host/device identifier |
IP addresses are required for communication on the internet, hosting a website, sending e-mail, of the cloud infrastructure and for cyberspace monitoring.
Why Users Search for 185.63.263.20

There are several reasons Indonesian users may search for this IP address.
Common Search Intent
| Search Purpose | Explanation |
| Security checks | Investigating suspicious activity |
| Website hosting lookup | Identifying server locations |
| Network troubleshooting | Diagnosing connectivity issues |
| Cybersecurity research | Analysing traffic logs |
| VPN or proxy detection | Checking anonymous server usage |
| Server reputation review | Determining trustworthiness |
IP searches have become more common as businesses and individuals monitor digital activity more closely.
How IP Addresses Work
Every internet-connected device connects using IP addresses.
Core Meanings of an IP Address
- Device identification
- Traffic routing
- Website hosting communication
- Network diagnostics
- Security filtering
- Data exchange
Without IP addressing systems, internet connectivity would not function efficiently.
Types of IP Addresses
Different categories of IP addresses exist depending on usage.
| IP Type | Purpose |
| Public IP | Visible on the internet |
| Private IP | Used inside local networks |
| Static IP | Permanent address assignment |
| Dynamic IP | Changes periodically |
| IPv4 | Traditional internet addressing |
| IPv6 | Newer large-scale addressing system |
185.63.263.20 follows the IPv4 format.
Possible Uses Associated With 185.63.263.20
An IP address can be linked with multiple internet services.
Potential Server Activities
| Possible Use | Description |
| Website hosting | Running websites or applications |
| VPN services | Anonymous browsing systems |
| Cloud infrastructure | Data storage or application hosting |
| Email servers | Sending or receiving mail |
| Proxy services | Traffic forwarding |
| Remote access systems | Device management connections |
However, an IP address alone does not automatically confirm harmful or safe activity.
Is 185.63.263.20 Safe?
Safety depends on the actual service, network owner, and server activity connected with the IP.
Important Security Considerations
Users should be cautious if:
- The IP appears in spam logs
- Antivirus software flags the address
- Unknown traffic originates from it
- Unexpected login attempts are detected
- Browser security warnings appear
Signs of a More Trustworthy Server
| Indicator | Explanation |
| HTTPS usage | Secure encrypted communication |
| Transparent hosting details | Public ownership information |
| Stable reputation | No major abuse reports |
| Secure certificates | Valid SSL/TLS security |
| Legitimate business association | Recognised services |
How Indonesian Users Can Check an IP Address
Several tools allow users to investigate IP details.
Common Lookup Information
| Data Type | What It Shows |
| Geolocation | Approximate server region |
| ISP/Hosting provider | Network owner |
| ASN details | Autonomous system information |
| Blacklist status | Spam or abuse reports |
| Open ports | Exposed services |
| DNS records | Domain associations |
These checks help users identify possible risks or hosting information.
Workflow: How to Analyse an Unknown IP Address
Step-by-Step IP Investigation Process
Step 1 — Copy the IP Address
Record the suspicious or unknown IP exactly.
Step 2 — Use an IP Lookup Tool
Search for hosting provider and geolocation information.
Step 3 — Check Reputation Databases
Review blacklist or spam detection databases.
Step 4 — Analyse Server Behaviour
Check for suspicious traffic patterns or login attempts.
Step 5 — Verify Associated Websites
Determine whether connected websites appear legitimate.
Step 6 — Monitor Security Logs
Continue monitoring if unusual activity persists.
This process helps reduce cybersecurity risks.
Common Cybersecurity Risks Linked to Unknown IP Addresses
Not every unknown IP is dangerous, but carefulness ruins significant.
Potential Risks
| Danger Type | Explanation |
| Phishing attacks | Fake login or payment systems |
| Malware delivery | Harmful software distribution |
| Brute-force login attempts | Password guessing attacks |
| Spam traffic | Bulk email abuse |
| Data scraping | Automated information collection |
| Bot activity | Automated malicious traffic |
Indonesian businesses increasingly monitor IP activity to protect online systems.
IP Addresses and Indonesian Internet Infrastructure
Indonesia has experienced rapid digital growth in recent years.
Internet Trends in Indonesia
| Area | Growth Trend |
| Mobile internet | Rapid expansion |
| Cloud services | Increasing adoption |
| Digital payments | Growing usage |
| Online businesses | Expanding market |
| Cybersecurity awareness | Improving steadily |
As internet activity increases, understanding IP-based systems becomes more important for users and organisations.
Comparison: IPv4 vs IPv6
| Feature | IPv4 | IPv6 |
|—|—|
| Address format | Numerical | Alphanumeric |
| Number of addresses | Limited | Extremely large |
| Compatibility | Widely used | Growing adoption |
| Complexity | Simpler | More advanced |
| Security improvements | Basic | Enhanced support |
Although IPv6 adoption is increasing, IPv4 addresses such as 185.63.263.20 remain common globally.
How Businesses Use IP Monitoring
Many organisations use IP monitoring for operational and security purposes.
Business Use Cases
| Industry | Usage Example |
| Banking | Fraud detection |
| E-commerce | Bot prevention |
| Hosting providers | Server monitoring |
| Schools | Network filtering |
| Government agencies | Security analysis |
IP intelligence has become an important part of digital risk management.
Expectations and Limitations of IP Lookup Results
Users should understand that IP lookup tools provide approximate information rather than perfect accuracy.
Important Limitations
- Geolocation may be inaccurate
- VPNs can hide real locations
- Shared hosting may involve multiple websites
- Dynamic IPs can change ownership
- Reputation databases may not update instantly
Therefore, IP information should be treated as guidance rather than absolute proof.
Best Security Practices for Indonesian Users
Suggested Online Safety Habits
| Repetition | Benefit |
| Use strong passwords | Account protection |
| Enable two-factor authentication | Extra security layer |
| Avoid suspicious downloads | Malware prevention |
| Monitor login activity | Early threat detection |
| Keep software updated | Reduced vulnerabilities |
Good cybersecurity habits help minimise risks linked to suspicious internet activity.
Future of IP Intelligence and Cybersecurity in Indonesia
Indonesia’s digital economy continues growing rapidly.
Expected Future Trends
- Increased cloud hosting adoption
- Improved cybersecurity regulations
- AI-powered threat detection
- Stronger data protection frameworks
- Expanded internet infrastructure
As cyber pressures evolve, IP intellect tools will likely become even more significant for businesses and individual users.
Conclusion
The word 185.63.263.20 is an IPv4 address which is expected to be used by server, website, cloud services or internet technology related activity. Users from Indonesia frequently search for IPs like this one when researching security issues, hosting provider info or diagnosing network problems.
Though can be valuable, user should not have unrealistic expectation on accuracy on IP lookup tools and should not be led into false conclusions based on geolocation or reputation alone, making a comprehensive IP check alongside good cyber security practices the safest strategy.
FAQ’s
What is 185.63.263.20?
185.63.263.20 is likely an internet address used for network communication or server hosting.
Is an IP address that accurate? Can it tell your location?
Most IP searches show a rough topographical region, not a bodily address.
Is 185.63.263.20 a danger?
An IP address in itself is not dangerous. The safety of this server depends on what activity and services it offers.
What tools can verify information available on IP address?
Further services include IP lookup, WHOIS database search, black list check and DNS analysis.
What are the differences between IPv4 and IPv6?
IPv4 uses a classic number-based address structure and IPv6 provides more numbers of addresses that can support for contemporary infrastructure.
Businesses should monitor stranger IP traffic?
Yes. It detects anything abnormality of traffic then it will improve the security and prevent for attack or unauthorize people.